1. Introduction to OSCP: The Gold Standard in Penetration Testing
The Offensive Security Certified Professional (OSCP), an ethical hacking certification offered by Offensive Security (OffSec), stands as a prominent credential in the cybersecurity domain. This certification is meticulously designed to validate an individual’s practical penetration testing skills, leveraging the tools and methodologies inherent in the Kali Linux distribution. The emphasis on hands-on expertise, rather than purely theoretical knowledge, distinguishes the OSCP as a rigorous and highly respected qualification for cybersecurity professionals seeking to demonstrate their capabilities in real-world scenarios.The OSCP has garnered significant recognition and a strong reputation within the cybersecurity field, emerging as a highly coveted credential for those specializing in penetration testing. Widely considered more technical than many other ethical hacking certifications, it uniquely demands that candidates provide tangible evidence of their practical penetration testing skills. This emphasis on demonstrable ability has led to the OSCP being frequently cited in job postings for roles such as ethical hackers, cybersecurity engineers, and penetration testers, signifying its value to employers seeking professionals with proven offensive security expertise. Recognizing the dynamic nature of the cybersecurity landscape, OffSec introduced the OSCP+ extension in November 2024. This updated certification requires renewal every three years, underscoring the necessity for cybersecurity professionals to engage in continuous learning and maintain current expertise in this rapidly evolving field.
2. Understanding the OSCP Exam Format and Scoring
The OSCP certification culminates in a rigorous, hands-on practical exam that spans 23 hours and 45 minutes, simulating a live network environment accessed through a private Virtual Private Network (VPN). This extended duration underscores the depth of assessment, requiring candidates to demonstrate both technical proficiency and the stamina to perform sustained penetration testing operations. The exam environment comprises a small number of vulnerable machines, specifically three standalone systems accounting for a total of 60 points, and one Active Directory (AD) set consisting of three interconnected machines valued at 40 points. Recognizing the complexity of modern network environments, the updated exam allows for the awarding of partial points for successful exploitation within the Active Directory domain.To achieve the OSCP certification, candidates must attain a minimum passing score of 70 points out of a possible 100. A critical rule of the exam is the restriction on the use of the Metasploit framework and the Meterpreter payload, which can only be employed on a single target machine of the candidate’s choosing. This limitation emphasizes the exam’s focus on manual exploitation techniques and a thorough understanding of vulnerabilities beyond automated tools. Following the intensive hands-on portion, candidates are allotted a subsequent 24 hours to meticulously document their findings in a comprehensive report, which is a crucial component of the overall evaluation.
| Exam Component | Details | Points |
| Standalone Machines (3) | Initial Access (10 points each), Privilege Escalation (10 points each) | 60 |
| Active Directory Set (3) | Machine #1 (10 points), Machine #2 (10 points), Domain Controller (20 points) | 40 |
| Total Points | 100 | |
| Passing Score | 70 |
3. Laying the Groundwork: Essential Skills and Knowledge for OSCP
Preparation for the OSCP exam necessitates a foundational understanding of several key areas. It is recommended that candidates possess a solid grasp of Transmission Control Protocol/Internet Protocol (TCP/IP) networking principles, as this knowledge is fundamental to understanding how systems communicate and where vulnerabilities might arise. Familiarity with scripting languages such as Python and Bash is also highly beneficial, as these skills are often required for automating tasks and modifying or creating exploits. Furthermore, practical experience in administering both Windows and Linux operating systems is crucial, as the exam environment typically includes machines running both platforms.Beyond technical prerequisites, a crucial element for success in the OSCP journey is adopting the “Try Harder” mindset championed by Offensive Security. This philosophy emphasizes the importance of persistence in the face of challenges, encouraging candidates to exhaust all possible avenues of investigation and to not be easily discouraged by setbacks. Creativity plays a vital role, requiring individuals to think outside conventional approaches and adapt their strategies to the unique circumstances of each target. Perceptiveness, the ability to observe subtle clues and piece together seemingly disparate pieces of information, is also key to identifying vulnerabilities that might be missed by more superficial assessments. This combination of persistence, creativity, and perceptiveness forms the core of the problem-solving approach that the OSCP exam seeks to evaluate.
4. Crafting Your OSCP Preparation Strategy
A well-defined preparation strategy is paramount for tackling the challenges of the OSCP exam. This involves leveraging official resources, engaging with practice labs and community platforms, and utilizing supplementary learning materials.
- Leveraging Official OffSec Resources:
- The cornerstone of any OSCP preparation plan should be the official Penetration Testing with Kali Linux (PEN-200) course. This comprehensive course provides a detailed guide in PDF format, accompanied by instructional videos that cover a wide range of penetration testing methodologies, tools, and techniques. Crucially, enrollment in the course grants access to a private lab environment, where students can apply the learned concepts through hands-on exercises and challenge labs on numerous vulnerable machines. Furthermore, the course includes access to a dedicated community forum, providing a platform for students to seek assistance, share insights, and collaborate with peers on their learning journey.
- Active participation in the lab exercises and diligent completion of the challenge labs are essential components of effective preparation, allowing candidates to translate theoretical knowledge into practical skills. In addition to the course and labs, the OSCP Exam Guide serves as a vital resource, outlining the specific rules, requirements, and expectations for the certification exam, including details on the exam format, scoring system, allowed tools, and reporting procedures.
- The Role of Practice Labs (PWK, Proving Grounds):
- The PWK lab environment is a significant aspect of the OSCP preparation, offering a diverse range of vulnerable machines that simulate real-world scenarios. This hands-on experience allows candidates to practice various penetration testing techniques and develop a deeper understanding of system vulnerabilities within a controlled setting.
- To further enhance practical skills, OffSec provides Proving Grounds , a subscription-based platform offering an even wider array of vulnerable machines. Proving Grounds is divided into Proving Grounds Practice, featuring machines designed by OffSec experts, and Proving Grounds Play, which includes community-contributed machines. This platform provides an excellent opportunity to test skills against a broader spectrum of challenges, often mirroring the difficulty and complexity of the OSCP exam itself.
- Exploring Community Platforms (Hack The Box, TryHackMe, VulnHub):
- Hack The Box (HTB) is a highly popular online platform within the cybersecurity community, offering a vast collection of vulnerable machines that simulate real-world security challenges. Practicing on HTB helps candidates refine their penetration testing skills and develop a more versatile approach to identifying and exploiting vulnerabilities. TJ Null’s curated list of OSCP-like boxes on HTB is a particularly valuable resource, guiding candidates towards machines that align with the difficulty and attack vectors typically encountered in the OSCP exam.
- TryHackMe (THM) provides a more structured and interactive learning experience, offering guided paths and labs on various cybersecurity topics, including penetration testing. THM is particularly beneficial for beginners as it often includes walkthroughs and hints, making it an excellent platform for building foundational skills before tackling the more challenging environments of PWK labs or HTB.
- VulnHub is a repository of downloadable vulnerable virtual machines that can be run locally, providing an offline environment for practicing penetration testing techniques. This can be particularly useful for individuals with limited or unreliable internet access, allowing them to continue their preparation without constant connectivity.
- Recommended Books and Courses:
- “Penetration Testing: A Hands-On Introduction to Hacking” by Georgia Weidman is widely recommended as an accessible and practical guide for individuals starting their journey into penetration testing, covering fundamental concepts and techniques relevant to the OSCP exam.
- For a deeper understanding of web application vulnerabilities, “The Web Application Hacker’s Handbook” is an invaluable resource, providing comprehensive coverage of common web security flaws and exploitation methodologies, which are frequently encountered in the OSCP labs and exam.
- To enhance skills in privilege escalation, a critical aspect of the OSCP, courses by The Cyber Mentor and Tib3rius on platforms like Udemy are highly recommended. These courses offer targeted training on both Linux and Windows privilege escalation techniques, providing practical insights and methodologies that can significantly improve a candidate’s ability to achieve root or administrator access on target systems.
| Resource Type | Resource Name | Description |
| Official Course | PEN-200 (Penetration Testing with Kali Linux) | Comprehensive course with labs, videos, and PDF guide by Offensive Security. |
| Practice Platform | OffSec Proving Grounds (Practice & Play) | Official practice labs with OffSec-designed and community-contributed machines. |
| Practice Platform | Hack The Box (HTB) | Online platform with a wide range of vulnerable machines; utilize TJ Null’s OSCP-like list. |
| Practice Platform | TryHackMe (THM) | Educational platform with guided learning paths and interactive labs, suitable for beginners. |
| Practice Platform | VulnHub | Repository of downloadable vulnerable virtual machines for offline practice. |
| Book | Penetration Testing: A Hands-On Introduction to Hacking by Georgia Weidman | Highly recommended book providing a practical introduction to penetration testing. |
| Book | The Web Application Hacker’s Handbook | Essential resource for understanding web application vulnerabilities and exploitation techniques. |
| Course | Practical Ethical Hacking by TCM Academy | Course covering foundational ethical hacking concepts, including Active Directory. |
| Course | Windows Privilege Escalation for OSCP & Beyond by Tib3rius | Udemy course focused on Windows privilege escalation techniques relevant to OSCP. |
| Course | Linux Privilege Escalation for OSCP & Beyond by Tib3rius | Udemy course focused on Linux privilege escalation techniques relevant to OSCP. |
5. Mastering Key Concepts and Techniques for the OSCP Exam
Success in the OSCP exam hinges on mastering several key concepts and techniques that are consistently tested in the lab environment and the certification exam.
- Effective Enumeration Strategies: Thorough enumeration is the cornerstone of any successful penetration test, and the OSCP exam is no exception. Candidates must be proficient in conducting comprehensive port scans using tools like Nmap to identify all potential entry points. This includes scanning both TCP and UDP ports, as overlooked UDP services can sometimes harbor critical vulnerabilities. Following port scanning, service enumeration is crucial to determine the specific applications and their versions running on the identified open ports. Understanding the services can provide valuable clues about potential vulnerabilities. For web applications, tools such as Nikto, Burp Suite, and DirBuster are essential for discovering hidden directories, files, and potential attack vectors. A systematic and exhaustive approach to enumeration is often the key to uncovering the initial foothold on a target system.
- Vulnerability Analysis and Exploitation: Once enumeration has yielded sufficient information about the target, the next step involves analyzing the gathered data to identify known vulnerabilities. Resources like the Exploit Database can be invaluable for finding existing exploits for specific software versions. However, the OSCP exam emphasizes the importance of understanding how these exploits work and often requires candidates to adapt or modify them to the specific target environment. Therefore, practicing manual exploitation techniques, rather than solely relying on automated tools, is critical for success. This deeper understanding allows for more effective troubleshooting and adaptation when encountering unexpected issues during the exploitation phase.
- Privilege Escalation (Linux and Windows): Gaining an initial foothold is often just the first step in the OSCP exam. The majority of the points are typically awarded for achieving root or administrator-level access on the target systems. Therefore, mastering privilege escalation techniques on both Linux and Windows platforms is paramount. Tools such as LinPEAS and WinPEAS can assist in identifying potential privilege escalation paths by automating the enumeration of misconfigurations, weak permissions, and other vulnerabilities that can be leveraged to elevate privileges. However, a solid understanding of the underlying operating system and common escalation vectors is essential for effectively utilizing these tools and for identifying less obvious pathways to root or administrator access.
- Active Directory Attacks: The inclusion of an Active Directory (AD) set in the OSCP exam necessitates a dedicated focus on AD attack methodologies. Candidates should practice techniques for enumerating the AD environment, identifying users, groups, and policies that might be vulnerable. Authentication attacks, such as Kerberoasting and AS-REP Roasting, can be effective ways to gain access to user credentials within the domain. Furthermore, understanding lateral movement techniques is crucial for navigating the AD environment and escalating privileges across multiple machines within the domain. The PWK course materials and dedicated labs provide a solid foundation for practicing these AD-specific attack vectors.
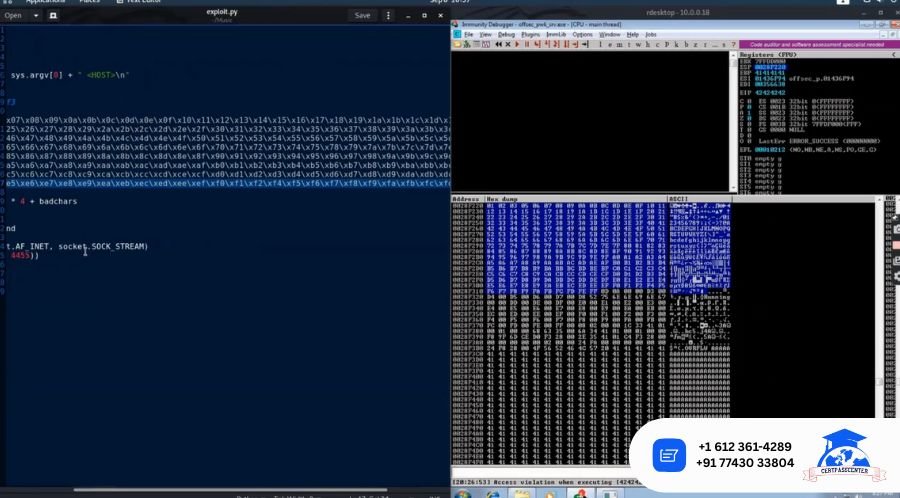
- Buffer Overflow Exploitation: While the emphasis on buffer overflow vulnerabilities might have shifted with the introduction of the AD set, it remains a relevant topic for the OSCP exam, often appearing as a low-privilege attack vector on one of the standalone machines. Candidates should practice identifying buffer overflow vulnerabilities, determining the offset to control the instruction pointer, and generating shellcode to achieve code execution. Familiarity with tools like Immunity Debugger and the process of identifying bad characters is essential for successfully exploiting buffer overflows in a controlled manner.
6. Navigating the OSCP Exam: Tips and Best Practices
The OSCP exam is not just a test of technical skills; it also assesses a candidate’s ability to perform under pressure and manage their time effectively. Several best practices can significantly enhance the chances of success.
- Time Management Strategies: Given the 23 hours and 45 minutes time limit for the hacking portion, effective time management is crucial. It is advisable to allocate a specific amount of time for each machine, taking into account its point value and perceived difficulty. Starting with the lower-point, potentially easier targets can help build momentum and secure some points early in the exam. It is also important to recognize when one is stuck on a particular machine and to pivot to another target rather than spending an inordinate amount of time on a single obstacle. Regular breaks are essential to avoid mental fatigue and maintain focus throughout the extended exam period. Stepping away from the screen, even for short intervals, can often provide a fresh perspective and help overcome roadblocks.
- Dealing with Exam Stress and Pressure: The OSCP exam is known for its challenging nature, and it is common for candidates to experience stress and pressure during the attempt. Maintaining a calm and composed mindset is vital for effective problem-solving. When encountering difficulties, it is helpful to take a step back, review the enumeration data, and approach the problem from a different angle. Taking short breaks can also aid in reducing anxiety and improving focus. Remembering that the exam is designed to be challenging and that getting stuck is a normal part of the process can help candidates persevere through frustrating moments.
- Avoiding Common Pitfalls and Rabbit Holes: One of the common pitfalls in the OSCP exam is getting stuck in rabbit holes – pursuing attack paths that ultimately lead nowhere. To avoid this, it is crucial to focus on thorough enumeration to identify all potential avenues of attack. If a particular approach is not yielding results within a reasonable timeframe, it is often best to pivot and try alternative methods. Overthinking the problem can also lead to missed opportunities. Sometimes, the most straightforward approach is the correct one. Maintaining a systematic methodology and documenting all attempts can help in recognizing when a path is unproductive and when it is time to shift focus.
7. Documenting Your Success: Writing a Comprehensive OSCP Exam Report
The OSCP exam culminates not only in the technical exploitation of target systems but also in the creation of a comprehensive penetration testing report. This report is a critical component of the evaluation process, demonstrating the candidate’s ability to clearly communicate their findings and methodologies. It is essential to meticulously document the entire process for each target machine, including every step taken, all commands issued, and the corresponding console output, accompanied by relevant screenshots.A key requirement is the inclusion of proof files – the contents of local.txt and proof.txt – which must be submitted through the exam control panel and also presented within the screenshots included in the report. Offensive Security provides official report templates in Microsoft Word and OpenOffice/LibreOffice formats , and candidates are highly encouraged to utilize these templates to ensure all necessary sections and information are included. The report should be written in a professional manner, detailing the steps taken from initial enumeration to final exploitation, allowing a technically competent reader to reproduce the candidate’s actions. Strict adherence to these reporting requirements is paramount, as insufficient or incomplete documentation can lead to a reduction in points or even failure of the exam.
8. Beyond the Exam: Continuous Learning and Community Engagement
Achieving the OSCP certification is a significant milestone in a cybersecurity career, but it is by no means the end of the learning journey. The field of cybersecurity is characterized by constant evolution, with new threats and vulnerabilities emerging continuously. Therefore, it is crucial for OSCP certified professionals to commit to continuous learning, staying updated on the latest trends, techniques, and tools in the offensive security landscape.Engaging with the cybersecurity community is an invaluable way to facilitate this ongoing education. The official OffSec community forums provide a platform for OSCP candidates and certified professionals to discuss challenges, share knowledge, and learn from each other’s experiences. Additionally, other online communities such as Reddit (specifically subreddits like r/oscp and r/netsec) and Discord servers offer real-time discussions, study groups, and collaborative problem-solving opportunities. Active participation in these communities not only provides support during the preparation phase but also fosters a network of peers and mentors who can contribute to continuous professional development.
9. Conclusion: Your Journey to OSCP Certification
The Offensive Security Certified Professional certification stands as a challenging yet highly rewarding pursuit for individuals aspiring to excel in the field of penetration testing. The rigorous hands-on exam and the comprehensive report writing requirement demand not only technical expertise but also a resilient and adaptable mindset. Embracing the “Try Harder” philosophy, combined with a well-structured preparation strategy that leverages official resources, practice labs, community platforms, and continuous learning, is the key to navigating the complexities of the OSCP journey. By dedicating time and effort to mastering the essential skills and techniques, and by meticulously documenting the learning process, aspiring OSCPs can confidently embark on this transformative path and ultimately achieve success in their pursuit of this esteemed certification.
Leave a Reply